Programming Services
- On-on-One Mentorship
- Question & Answer
- On-demand Programming
- Project-based Freelance Work
Experienced Engineers
From Top Ranked Tech Companies
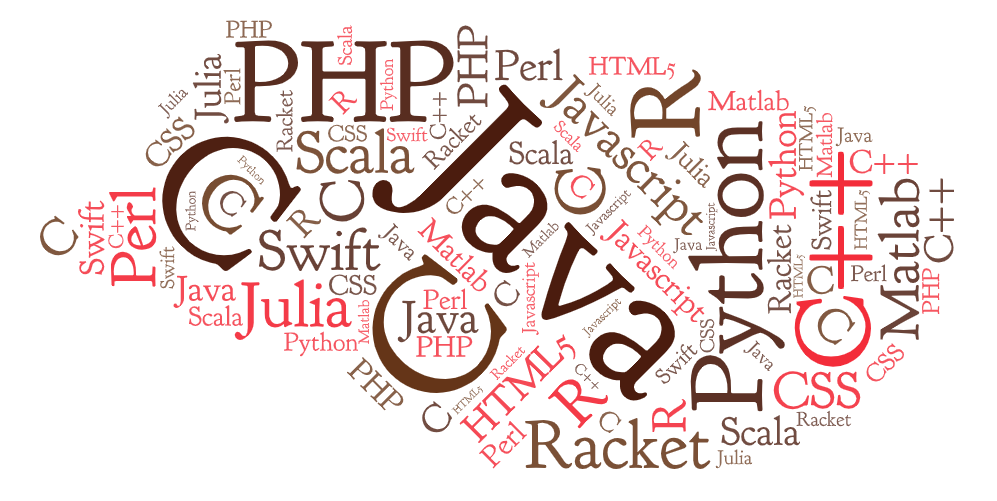
Programming Subjects of Expertise
CS304 Individual Assignment 1: Add New Features to Teedy
In this assignment, you will add some new features to Teedy, which will help you learn how to navigate and understand complex codebases.
COMP 315: Cloud Computing for E-Commerce - Assignment 1: Javascript
A common task when backend programming is data cleaning, which is the process of taking an initial data set that may contain erroneous or incomplete data, and removing or fixing those elements. In this assignment, you will be tested on your knowledge of JavaScript by implementing a set of functions that perform data cleaning operations on a dataset.
CS3388B - Computer Graphics Assignment 4: Textured Triangle Mesh
The goal of this assignment is get comfortable with triangular meshes and working with the camera in world space.
COMP4436 AIoT Assignment I - Comparative Analysis of ML, DL and SNN Algorithms in AIoT Applications
The goal of this assignment is to implement and compare the performance of various machine learning (ML) and deep learning (DL) algorithms, including a spiking neural network (SNN), in the context of an Artificial Intelligence of Things (AIoT) application
COMP4436 Artificial Intelligence of Things - AIoT Assignment - Comparative Analysis of ML, DL and SNN Applications lgorithms in AIoT
The goal of this assignment is to implement and compare the performance of various machine learning (ML) and deep learning (DL) algorithms, including a spiking neural network (SNN), in the context of an Artificial Intelligence of Things (AIoT) application.
ECS 034: Software Development in UNIX & C++ - Project 2: CDSVReader and CDSVWriter
You will be implementing and documenting several C++ classes to generate and parse both delimiter-separated-value (DSV) and XML files. To guide your development and to provide exposure to Test Driven Development, you will be developing GoogleTest tests to test your classes.
EECS 183 Elementary Programming Concepts - Project 2: Rock-Paper-Scissors
In this project, you will be implementing a rock-paper-scissors game! Rock-paper-scissors is a hand game played between two people, in which each player simultaneously forms one of three shapes with an outstretched hand. These shapes are “rock” (a simple fist), “paper” (a flat hand), and “scissors” (a fist with the index and middle fingers extended, forming a V).
EECS 183 Elementary Programming Concepts - Project 1: Focaccia Bread
In this project, you will write a program to help you purchase the correct amount of ingredients to make focaccia bread for a party.
CS202 Operating Systems - Lab 4: File Recovery
In this lab, you will work on the data stored in the FAT32
CS1026A Computer Science Fundamentals I - Assignment 3: YouTube Emotions
Our goal in this assignment is to use a simplified version of the NRC Emotion Lexicon to classify YouTube comments based on one of the following emotions anger, joy, fear, trust, sadness, or anticipation. Based on the emotion contained in each comment for a particular video we then want to generate a report that details the most common emotions YouTube users have towards that video based on their comments.
EE4204/TEE4204 Computer Networks (Part 1) - Socket Programming Assignment (Sem1, 2024-25)
Develop a TCP-based client-server socket program for transferring a large message. Here, the message transmitted from the client to server is read from a large file. The message is split into short data-units which are sent by using stop- and-wait flow control. Also, a data-unit sent could be damaged with some error probability.
ITD103 IT Systems Design - Assessment Task 3 - Design Challenge 2
This is a case-based assessment. Most of the tasks need to be completed based on the IT cases that have been provided in this document. We also have provided templates for your answers (available on Canvas). This assessment focuses on the analysis and design of the structure of an information system.
ECE 4122/6122 Advanced Programming Techniques - Lab 1: Retro Centipede Arcade Game
Create a simple version of the classic arcade game called Centipede. An online version of the game can be found at (https://www.mysteinbach.ca/game- zone/2153/atari-centipede/). The goal of the assignment is to try to reproduce the game play present on the listed web site
CSSE2310/CSSE7231 Computer Systems Principles and Programming - Assignment 4: Chess Server
The goal of this assignment is to further develop your C programming skills, and to demonstrate your under- 2 standing of networking and multithreaded programming. You are to create a server program (uqchessserver) 3 that supports multiple simultaneously connected clients playing chess against another client or against a chess 4 engine (Stockfish).
CS544 Intro to Big Data Systems - P4: HDFS Partitioning and Replication
In this project, you'll deploy a small HDFS cluster and upload a large file to it, with different replication settings. You'll write Python code to read the file. When data is partially lost (due to a node failing), your code will recover as much data as possible from the damaged file.
DPST1091/CPTG1391 Programming Fundamentals! - Assignment 2 - CS Pet Salon
Your task is to implement a pet salon manager involving several salons which have rooms for different types of pets. A pet salon is where pets get cared for and pampered. You will track the details of the pets being looked after in each salon!
DPST1092 Computer Systems Fundamentals - Assignment 2: a file synchroniser - rsync
The rsync utility is a useful and popular tool which efficiently transfers files between computers. In this assignment you will be implementing rbuoy, which is a simplified version of rsync.
CS537 Introduction to Operating Systems - Project 4: Dynamic Stride Scheduler with Dynamic Ticket Modification
In this project, you will implement a dynamic stride scheduler in xv6, incorporating dynamic ticket modification based on process behavior. The stride scheduler ensures that processes receive CPU time proportional to their assigned tickets, providing deterministic scheduling behavior. By dynamically adjusting tickets, the scheduler can adapt to changing process workloads, priorities, or resource usage.
EECS 183: Elementary Programming Concepts - Project 4: CoolPics
In this project, you will create a program that reads in a description of shapes, draws those shapes, and saves the result to a file. You will represent the different shapes using classes. Here are some examples of images created by students in past semesters:
EECS 183: Elementary Programming Concepts - Final Project: Elevators
Elevators is a project that dabbles in Game Design, Artificial Intelligence, and designing real-world systems. Using C++, you will complete an implementation for a game in which the player operates 3 elevators in a busy building, making decisions and servicing requests to keep the people inside the building as happy as possible.
CS460 Introduction to Database Systems - Problem Set 3 - Implement portions of a simple relational database management system
In this assignment, you will implement portions of a simple relational database management system that supports a subset of the SQL language
COMP1511 Programming Fundamentals - Assignment 2 - CS Dungeon!
Your task in assignment 2 is to create a dungeon crawler game, where you will get to design a map of connected dungeons filled with monsters, items, and a final boss at the end to defeat! You will get to play as either a Fighter or a Wizard, using your special skills and stats to defeat these monsters and beat the game!
ELEC576/COMP 576: Introduction to Deep Learning Assignment 1 - Backpropagation
In this problem, you will learn how to implement the backpropagation algorithm for a simple neural network. To make your job easier, we provide you with starter code in three layer neural network.py. You will fill in this starter code to build a 3-layer neural network (see Fig. 1) and train it using backpropagation.
Concurrent Programming Coursework 2024 - Prefix Scan Algorithm in C/MPI
You are required to implement the parallel prefix scan algorithm in c/mpi
CS321: Programming Languages - Homework 2: Functions, Errors, Conditionals, Predicate and Multiplication
Start with the f1WAE interpreter for deferred substitution, and extend the implementation to support any number of arguments to a function (including zero), and any number of arguments (including zero) in a function application:
CPS 112: Computational Thinking with Algorithms and Data Structures Homework 3 - Fly Away Home
For this assignment you will develop a simple game called “Fly Away Home.” The basic idea behind the game is to safely move Mosca around a grid to the home square before he gets eaten. The user will control the movements of the fly using arrow keys, and the frogs will move on their own. I have provided you with most of the GUI implementation. In the rest of this description are the pieces you need to implement.
31927 Applications Development with .NET - Assignment 2 - GUI
This assessment requires you to develop an application with the necessary graphical user interface - GUI (e.g., Windows Form) and underlying functionality based on your proposed topic. This is a group assignment, and each group should ideally consist of a minimum of two and a maximum of three students.
EE658 Diagnosis and Design of Reliable Digital Systems - Fault Simulation Group Project Phase #2 - DFS and FPS
The second phase of the group project focuses on the implementation of two different fault simulation methods: deductive fault simulation (DFS) and parallel fault simulation (PFS), applying techniques to reduce the fault list in a netlist, and also a few modifications to your previously developed logic simulator.
CSCI-1200 Data Structures - Fall 2024 Homework 6 - Recursive Kurotto Solver
In this homework we will develop a solver for a paper-and-pencil puzzle game named Kurotto. The input to Kurotto is a 2D rectangular grid where all the cells are initially water. Some of the cells in the grid are labeled with a non-negative integer.
CPT205 Computer Graphics - Assessment 1 - 2D Modelling Project - Birthday Card
You are required to create a two-dimensional (2D) Birthday Card. Your card may contain balloons, flowers, trees, smiling faces, lights, stars, clouds, sky, ground, buildings and other objects that may appear in a physical card of this kind
Assignment: Denoising Diffusion on Two-Pixel Images
The field of image synthesis has evolved significantly in recent years. From auto-regressive models and Variational Autoencoders (VAEs) to Generative Adversarial Networks (GANs), we have now entered a new era of diffusion models. A key advantage of diffusion models over other generative approaches is their ability to avoid mode collapse, allowing them to produce a diverse range of images.
CISC422/CMPE 422: Formal Methods in Software Engineering (Fall 2024) - Assignment 2: Class Modelling with Alloy
This assignment uses Alloy, an analysis tool for class models developed by the Software Design Group at MIT. Alloy is publicly available for Windows, Linux and Mac OS and there is extensive documentation for it, including a book, a collection of sample models, and the Stack
FIT9132 Introduction Databases - Assignment 2 - Creating, Populating and Manipulating Databases - Paris Arrow Transit (PAT)
Your task for this assignment is to design a model for Paris Arrow Transit (PAT). Paris Arrow Transit is a private company subcontracted by the Olympic Federation to transport officials during the Olympic competition. The company realises that it needs a completely new computerised system to more efficiently manage and record its services during the Games. You have been asked to develop a database system that can meet PAT's needs, which are detailed below.
MXB261 Modelling and Simulation Science - Assignment 2 - A Simulation Project - Modelling an Epidemic
The theme of this project is the effect of parameter values on the behaviour of a viral epidemic a mathematical model, in both a temporal and spatial setting.
CSC3100 Data Structures Fall 2024 Programming - Assignment 2: Queue and Time Complexity
Given an n-length list, the value ai in the list satisfies that ai ∈ {1, ..., n} and i = 1, ..., n. Then, numbering each element ai in the list as bi, bi = i. Please find the minimum number of elements that should be deleted so that the list of remaining elements has the same elements as the list of their corresponding numbers.
ECE4122/ECE6122 Advanced Programming Techniques for Engineering Applications - Lab 3: OpenGL with OBJ files and Multiple Objects
To create a dynamic 3D graphics application using lighting, shading, model transformations, and keyboard inputs.
COP3502 Programming Fundamentals I - P2: RLE with Images Python
In this project students will develop routines to encode and decode data for images using run-length encoding (RLE). Students will implement encoding and decoding of raw data, conversion between data and strings, and display of information by creating procedures that can be called from within their programs and externally. This project will give students practice with loops, strings, Python lists, methods, and type-casting.
PITT CS445 Algorithms and Data Structures I Project 2: LinkedDS
This project is designed to increase your experience with linked data structures. Similar to Project 1, you will work with control structures, class-building, interfaces, and generics to create a new linked data structure called a LinkedDS<T>. The LinkedDS<T> will implement the SequenceInterface<T>, so before doing anything else, take a look at the method comments in SequenceInterface.java.
CS460 Introduction to Database Systems - Problem Set 2 - Converting the Oscar table to XML
In this problem, you will write a series of methods that can be used to create an XML version of the Oscar table from Problem Set 1. Your methods will be part of a larger program that uses the JDBC framework to connect to the SQLite database that you used in PS 1 and to execute the SQL queries needed to extract the necessary data.
COM661 Full Stack Strategies and Development - Assignment 1: Backend
Over the course of the module, we construct the Biz Directory - a sample full stack application built around a database containing information on a range of businesses and a collection of user- contributed reviews. This assignment tests your understanding of this material by having you build the back-end of your own full stack application, based around a dataset of your choice
DTS201TC Pattern Recognition - Coursework - Covid-19 CT Image Data Classification Using Principal Component Analysis
This coursework is the assessment for DTS201TC and aims to evaluate understanding of pattern representation, feature discovery and selection, foundations of pattern recognition algorithms and machines including statistical, structural and neural methods.
EF4323 Trading Room Workshop - Algorithmic Trading Project
In this project, we simulate the algorithmic trading business model, where a small group of proprietary traders tries to attract outside institutional investment by marketing their trading strategies and performance.
CS439 Introduction to Data Science - Homework 1: MapReduce, Association Rules, Locality-Sensitive Hashing
Write a MapReduce program in Hadoop that implements a simple “People You Might Know” social network friendship recommendation algorithm. The key idea is that if two people have a lot of mutual friends, then the system should recommend that they connect with each other.
CS 245 Advanced Programming and Data Structures - Assignment 2 - Mouse Simulation
This assignment will have you practice developing an OOP as a Java solution and have safe trip . You are to write classes that define a Mouse, Mouse.java, and a Cat, Cat.java
TCS3294 Windows Programming - Assignment: Gym Management System
The aim of the assignment is to expose students to analyse a variety of problem solutions in terms of the design concepts and programming constructs. This assignment will allow the students to produce appropriate system development documentation with complete program using C#.NET Framework programming language and SQL Server. The students should be able to apply their knowledge and skills, creativity, and critical thinking in completing the assignment.
COMP3506/7505 - Algorithms and Data Structures - Assignment Two: Bloom Filter, Pathfinding, Chain Reaction
The main objective of this assignment is to extend your knowledge from assignment one to build more complex data structures and solve more complex problems
CMU 95-702 Distributed Systems for ISM - Project 2 Client-Server Computing
In Task 0, you will make several modifications to EchoServerUDP.java and EchoClientUDP.java. Note that these two programs are standard Java and we do not need to construct a web application in IntelliJ. Both of these programs will be placed in the same IntelliJ project.
CMU 95-702 Distributed Systems - Project 1: Compute Hash
In this assignment, you'll build several web apps to gain more experience. You build your first set of distributed systems. These are two small web applications using Servlets and Java Server Pages.
ITECH3108 Dynamic Web Development - Assessment 1 - Front-end Development
For this assessment task, you will use skills acquired through the first six weeks of material to build an interactive front-end to an API. You will be developing a front-end for a simple forum application, using front-end JavaScript, the Document Object Model, and fetch to connect to a RESTful web API. You will also submit a written reflection on your learning.
CS 520 Introduction to Operating Systems - Homework 3: Bus Simulation
Write the bus simulation, as explained in the class and described in the notes. Feel free to look on the web for and then re-use any suitable code for the random number generator or for linked list algorithms. With that, 1) don’t forget to include a reference to the source of any code you re-use and 3) remember to test all re-used code as you are the only one responsible for its performance..
COMP3702 Artificial Intelligence - Assignment 3: Reinforcement Learning
In this assignment, you will implement Deep Reinforcement Learning algorithms and analyse their parameters and performance. This assignment will test your skills in training and understanding reinforcement learning algorithms for practical problems and understanding of key algorithm features and parameters.
JC4003: Natural Language Processing - Group Assessment: Understanding and Generating Explanations from the RuozhiBa Dataset
In this group assessment, you will explore and experiment with traditional machine learning and deep learning models, including large language models (LLMs), to generate accurate meanings and explanations for the samples provided in the RuozhiBa dataset. The purpose of this exercise is to apply your knowledge from the course to a real-world dataset, practicing your skills in data annotation, model design, and evaluation.
CMU 95-702 Distributed Systems For Information Systems Management - Project 3 Blockchain and Signatures
In this project, we will illustrate an important nonfunctional characteristic of blockchain technology - its tamper evident design. We will build a stand-alone blockchain in Task 0 and a distributed system where a remote client interacts with a blockchain API in Task 1. In Task 2, we will work with digital signatures.
CT047 Systems Programming and Computer Control - Assignment - Smart Home Controller
A company has received a contract to design a controller for a Smart Home. A Smart Home is a home fitted with controllers and sensors which permit remote control and automation. The specifications and rules are listed below. Your job is to design a controller using LabVIEW that satisfies all specifications.
COMP10002 Foundations of Algorithms - Assignment 2: Dynamic memory and Cellular Automaton
In this project, you will demonstrate your understanding of dynamic memory and linked data structures (Chapter 10) and extend your program design, testing, and debugging skills. You will learn about cellular automata, implement a tool for performing cellular automata computations, and use this tool to solve a practical problem.
FIT3003 Business intelligence and data warehousing - Assignment 2: M-Stay Residential Service
M-Stay is a residential service that offers homestay and rental services to Monash students and staff around Melbourne. The company has an existing operational database that maintains and stores all of the business transactions information (e.g. properties, hosts, listings, booking, etc.) required for the management's daily operation. As the business grows, M-Stay has decided to build a Data Warehouse to improve their analysis and work efficiency. However, since the staff at M-Stay have limited Business Intelligence and Data
COMP1521 Computer Systems Fundamentals - Assignment 1: Nonograms in MIPS
nonograms.c is an implementation of a program to play nonograms (also known as Picross). A nonogram puzzle takes place on a 2D grid, where the player must mark a set of cells, according to number clues placed on the edge of the puzzle.
CS-350 - Fundamentals of Computing Systems Homework Assignment #4 - BUILD
To improve throughput and utilize system resources more efficiently, you’ll now modify your server to process requests using multiple worker threads. The new server will still allow to specify a maximum queue size to limit its maximum workload.
COMP1511 Programming Fundamentals - Assignment 1: Moonlander
Moonlander is a small game where the player enters commands to move an astronaut around the moon to collect moon cheese, without running out of oxygen. The aim of the game is to collect some target amount of cheese and make it back to the lander to export the moon cheese back to Earth! Movement has an oxygen cost and to collect the cheese we may have to navigate around rocks and avoid running out of oxygen completely (a player can drop off cheese and refill their oxygen tank at the lander
COMP338 Computer Vision - Assignment 1- Canny Edge Detection, Feature Extraction
OpenCV provides a function canny() to get the edge detection result with an image (you can use any grey image). Please do the following: (25 marks) Reimplement the canny operation without using the built-in canny() function (with some explanations of the code). (10 marks) Test and visualize your implementation results. (with different filters, different thresholds and others) (15 marks) Discuss the difference between your implementation, your results compared with the OpenCV implementation. (Compare the numerical results and the running time and others.)
CS544 Intro to Big Data Systems - P3: Large, Thread-Safe Tables
In this project, you'll build a server that handles the uploading of CSV files, storing their contents, and performing operations on the data. You should think of each CSV upload as containing a portion of a larger table that grows with each upload.
CS 660 Graduate Introduction to Database Systems - Programming Assignment 2 - B+ Tree
In this assignment, we will implement a file with a tree index. The file will store tuples in sorted order and the index will allow us to quickly find tuples based on an integer key.
DPST1091/CPTG1391 Programming Fundamentals - Assignment 1: Sokoban
Sokoban is a simple Japanese puzzle game from the 80's, although the rules are simple, levels can be deceptively hard. The main idea of Sokoban is a small grid board, containing walls, boxes, storage locations and a single player. The player moves around the board pushing boxes around until they manage to get all boxes stored in one of the storage locations! Feel free to check out the wikipedia entry for Sokoban too. For this assignment, you will be building both a level generator for the game, as well as the mechanics to play your created levels!
EECS 183 Elementary Programming Concepts - Project 3: Ciphers
In this project, you will move on to cryptography and you’ll be asked to encrypt and decrypt messages using three different encryption algorithms. The S’more part of this project will challenge you to “crack” others’ secret messages in ciphertext and convert them back to plaintext.
CITS3402 High Performance Computing - Assignment - Sparse matrix-matrix multiplication using MPI and OpenMP
Your task is to implement the matrix-matrix multiplication algorithm using MPI and OpenMP taking two sparse matrices in the matrix market representation as the input.
CS 188 Introduction to Artificial Intelligence - Project 3: Reinforcement Learning
In this project, you will implement value iteration and Q-learning. You will test your agents first on Gridworld (from class), then apply them to a simulated robot controller (Crawler) and Pacman.
COMP3411/9814 24T3 Artificial Intelligence - Assignment 1: Artificial neural networks
In this assignment, you will use artificial neural networks for drought modelling in the Murray-Darling Basin. You will conduct two tasks: (a) A classification task to predict whether there is ‘a drought’ or ‘no drought’ based on the climate conditions. (b) A regression task to predict the intensity of a drought based on the climate conditions.
CSEE4119 F24 Computer Networks Project 1: Video CDN
In this project, you will explore aspects of how streaming video works, as well as socket programming and HTTP. In particular, you will implement adaptive bitrate selection. The programming languages and packages are specified in the development environment section.
CSC148 Introduction to Computer Science - Assignment 2: A Treemap Visualiser
For this assignment, you will write an interactive treemap visualisation tool that you can use to visualise hierarchical data. It will have a general API (imple- mented with inheritance, naturally!) and you will define specific subclasses that will allow you to visualise two different kinds of data: the files and folders in your computer, and a categorization of Computer Science Education research papers.
CSC343 Introduction to Databases - Assignment 2 - Warmup
In this assignment, we will work with a database for a veterinary clinic, with a similar but not identical schema to the one you saw in Assignment 1. Keep in mind that your code for this assignment must work on any database instance (including ones with empty tables) that satisfies the schema.
CY 5010 Cybersecurity Principles and Practices - Lab 2: Cryptosystem Implementation
In this lab assignment, you will implement a cryptographic scheme intended to provide the most important protections for preserving chain of custody of a digital evidence. Your scheme must provide integrity and non-repudiation among the custodians involved, and also the communication with a central ledger, which implements a hash chain of the custodian signatures preventing the modification of the records.
BFF5555 Financial machine learning - Project: Predict positive market movements
You are required to develop a machine learning model to predict positive market movements (uptrend). This prediction task will be treated as a binary classification problem, where the target variable is binary [0, 1].
COMP3095 Web Application Development Using Java - Assignment 1: Room Booking and Event Management System
The goal of this assignment is to design and implement a microservices-based room booking and event management platform for George Brown College. Your platform should allow students, staff, and faculty to book room resources for events and meetings. The focus will be on microservices creation, database integration using JPA, inter-service communication, containerization with Docker, and integration testing.
COMP517 Data Analysis - Lab 9: Introduction to One-way ANOVA and Simple Linear Regression
In this lab, we introduce the fundamental concepts of hypothesis testing using one-way analysis of variance (ANOVA) and simple linear regression models. We will use ANOVA statistical techniques to analyze exam scores across various streams of students.
CSC 485H/2501H: Computational linguistics, Fall 2024 - Assignment 2: The Lesk algorithm & word2vec, BERT and Transformer
Recall the problem of word sense disambiguation (WSD): given a semantically ambiguous word in context, determine the correct sense. A simple but surprisingly hard-to-beat baseline method for WSD is Most Frequent Sense (MFS): just select the most frequent sense for each ambiguous word, where sense frequencies are provided by some corpus
FIT2014 Theory of Computation - Assignment 2- Regular Languages, Context-Free Languages, Lexical analysis, Parsing, Turing machines and Quantum Computation
In these exercises, you will: implement a lexical analyser using lex (Problem 3); implement parsers using lex and yacc (Problems 1–6); program a Turing machine (Problem 7);
FIT2004 Algorithms and data structures - Assignment 2: A Fun Weekend Away and Customised Spell Checker
Given all the hard work during the semester, you and your friends decided that you should better get a weekend off after Week 12 before starting preparing for your final exams. Your plan is to do some fun activity (e.g., surfing, hiking, kayaking, mountain biking, etc.) during this weekend getaway
INFO1113 COMP9003 Object-Oriented Programming - Assignment: Ink Ball
In this assignment, you will create a game in the Java programming language using the Processing library for graphics and gradle as a dependency manager. In the game, balls spawn and move around the screen and the player can draw lines to direct them into holes of the same colour. When balls are reflected off a player-drawn line it disappears. If a ball enters a hole of a wrong colour, score is lost and it respawns. Once all balls are captured by holes, the player wins.
CSC 485H/2501H: Computational linguistics, Fall 2024 - Assignment 1: Transition-based dependency parsing and Graph-based dependency parsing
Dependency grammars posit relationships between “head” words and their modifiers. These rela- tionships constitute trees where each word depends on exactly one parent: either another word or, for the head of the sentence, a dummy symbol, “ROOT”. The first part of this assignment concerns a parser that builds a parse incrementally
ECE 4016 Computer Networks - Assignment 1: Local DNS Server
In this assignment, you are required to implement a simple Local DNS Server
CS112 Lab 09: Neural Networks
Later this semester, you will create a working neural network in Java, using only your own code. In later classes, you will probably use neural network libraries developed by others to learn about many facets of Machine Learning. But in this class, you will learn that there is no magic in making a neural network— it is something you can build yourself...though the fact that neural networks perform so well does seem like magic.
Computer Science 320SC Applied Algorithmics - Programming Assignment 5: Finding partner and Killing enemies.
This 5th assignment lets you get familiar with dynamic programming design and development. It is worth 5% of your total course marks. We would like you to implement efficient dynamic programming algorithms for two tasks: Task 1: Finding partner and Task 2: Killing enemies.
COMP 348 Principles of Programming Languages - Assignment 1: The C Programming Language
In this assignment, you will gain hands-on experience with the C programming language. While you are not required to be a C expert to complete the work, you will certainly have the opportunity to explore most of the things that we have discussed in class (and a few other things as well). In terms of your task, you will be creating a simple “spreadsheet” application that can be used to calculate and display final grades in COMP 348
COMP30026 Models of Computation - Assignment 2: Regular Languages, DFA Construction, Context-Free Languages, Closure Properties and Pumping Lemma
To improve your understanding of formal languages, automata, and grammars; to develop your skills in analysis and formal reasoning about complex concepts, and to practise writing down formal arguments with clarity.
COMP3230 Principles of Operating Systems - Programming Assignment One: Implement a LLM Chatbot Interface
The goals of this programming exercise are: To have hands-on practice in designing and developing a chatbot program, which involves the creation, management and coordination of processes.
CS152 L3D Learning from Limited Labeled Data - HW1: Transfer Learning for the Birds
In this HW1, you'll apply Transfer Learning to a real dataset, and wrestle with several questions: Problem 1: For a specific target classification task of interest, would we rather have a source model trained on a "generic" dataset like ImageNet1k, or a smaller dataset related to our target task? Problem 2: What are the tradeoffs between fine-tuning just the last layer (aka "linear probing") and fine-tuning a few more layers? Can we compose these to do better?
CIT 593 Introduction to Computer Systems - Module 06 Assignment: While Loop, Subroutine, Data Memory and Pointers
In this assignment, we will start programming in the LC4 assembly language. We also introduce PennSim, a computer that can assemble and run LC4 programs. Finally, we introduce Codio, a remote hosted Linux platform that provides a standardized environment to ensure consistent grading.
CS 135 Intro to Machine Learning - Project A: Classifying Sentiment
As a team, you will work on one semi-open problems, and then a completely open problem. The 2 problems look at different representations of text for a common task. Problem 1 looks at using bag-of-word feature representations Problem 2 is an open-ended problem, where any feature representation is allowed
COMP9414 Artificial Intelligence - Assignment 1: Constraint Satisfaction Search
More technically, this assignment is an example of a *constraint optimization problem*, a problem that has constraints like a standard Constraint Satisfaction Problem (CSP), but also *costs* associated with each solution. For this assignment, we will use a *greedy* algorithm to find optimal solutions to visitor hosting problems that are specified as text strings.
CS380I Programming Assignment 2: LiveOak - 2 to SaM Compiler
Create a handwritten recursive-descent parser and SaM code generator for levels 0, 1, and 2 of the LiveOak language.
CS 135 Intro to Machine Learning - Homework 2: Evaluating Binary Classifiers and Implementing Logistic Regression
In this HW, you’ll complete two problems related to binary classifiers. In Problem 1, you’ll implement common metrics for evaluating binary classifiers. In problem 2, you’ll learn how to decide if a new feature can help classify cancer better than a previous model. As much as possible, we have tried to decouple these parts, so you may successfully complete the report even if some of your code doesn’t work. Much of your analysis will use library code in sklearn with similar functionality as what you implement yourself.
CS152 L3D Learning from Limited Labeled Data - HW2: SSL to the Moon
In this HW2, you'll implement a common method for each style of SSL, (self- and semi-), and then evaluate your implementation on a toy dataset. Problem 1: Establish a baseline for supervised training on labeled-set-only. Problem 2: Can we gain value from pseudo-labeling? Problem 3: Can we gain value from SimCLR?
CIT 593 Introduction to Computer Systems - Module 07 Assignment: TRAPs and memory-mapped devices
In this assignment, you will continue programming in LC4 Assembly. We will be working in the Operating System portion of memory, so you will learn about TRAPs and memory-mapped devices.
COMP2400/6240 Relational Databases Semester 2, 2024 Assignment 2 (Database Theory)
FlyHigh is an airline company that specializes in providing on-demand charter flight services. The company operates a fleet of ten aircraft, catering to a diverse range of customers who require flexible and personalized flight options. To effectively manage its operations, FlyHigh maintains records for each customer, including their unique customer number, full name, contact phone number, and residential or business address.
COMP5216 Mobile Computing - Assignment 2: Develop a media recording app
Camera and Location are two of the most frequently used sensors on an Android device. In this assignment, you are required to write an app that enables the user to take a video or photo and then upload it to Google’s Firebase cloud server for backup
SWD604 Program Design and Construction - Assignment 2: Admin Panel
You have been hired as an intern at Ahera Taera and have completed the creation of a customer management system for Ahera Taera, a new retail outlet focusing on a varied range of customers from senior citizens to kids. Considering all the requirements were successfully completed by you, the manager and the team has hired you to develop the next project phase. You are entrusted to develop an admin panel for the already developed software.
COMP5511 Artificial Intelligence Concepts - Assignment 1: TSP, GA, Dynamic Optimization and Multi-objective optimization
Traveling Salesman Problem (TSP) is a classical combinatorial problem that is deceptively simple. This problem is about a salesman who wants to visit n customers cyclically. In one tour, the salesman must visit each customer just once and should finish up where he started
5SD814 Programming with C/C++ 4: Computer Games in 2D - Assignment 2: COLLISION DETECTION
The Separating Axis Theorem (SAT) provides a powerful and efficient method for detecting collisions between convex polygons in 2D (and 3D). A convex polygon is a shape where all internal angles are less than or equal to 180 degrees, ensuring it "bulges outwards" rather than inward. SAT simplifies collision detection by focusing on finding one axis (a line) along which the two shapes do not overlap.
COMP2404AB (Fall 24) Introduction to Software Engineering - Assignment 1: Campground
In this assignment you will make a basic CRUD (create, read, update, delete) application. You will learn the basics of classes, arrays, and static memory in C++. You will make a few simple classes, populate the members using constructors and write functions to process the data. You will learn how to provide a working Makefile, and implement a small amount of application logic.
CS 0445 Algorithms and Data Structures I Project 1: ReallyLongInt
Design and implement a generic class (ArrayDS<T>) that will act as a data structure for accessing sequences of Java Objects. Your ArrayDS<T> class will primarily implement 2 interfaces – SequenceInterface<T> and ReorderInterface. The details of these interfaces are explained in the files SequenceInterface.java and ReorderInterface.java. Read these files over very carefully before implementing your ArrayDS<T> class.


